
GhostWare Injector
Full-Stack Architectural Override
HIJACK THE
COMPILATION PIPELINE
[ DOWNLOAD V4.0 APK ]
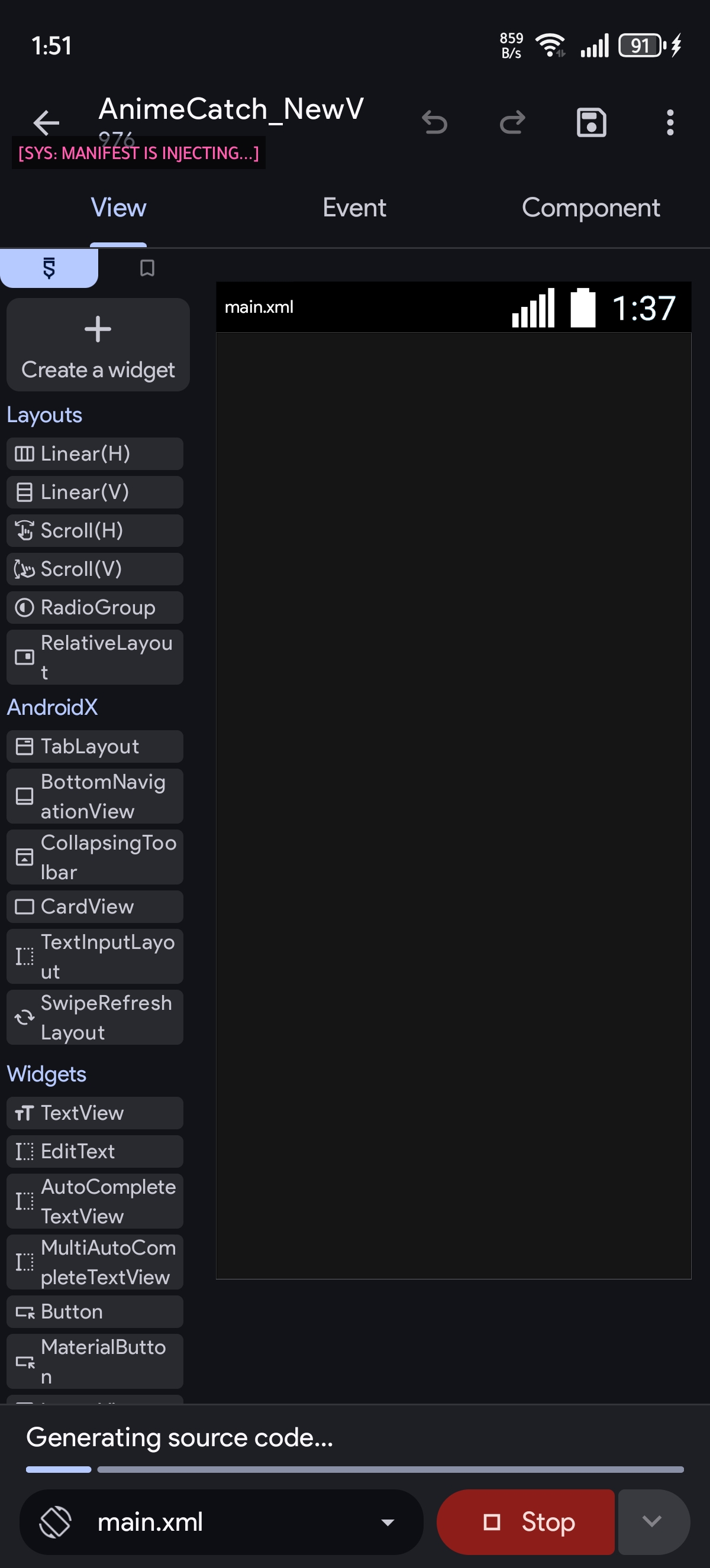
Interface Overview
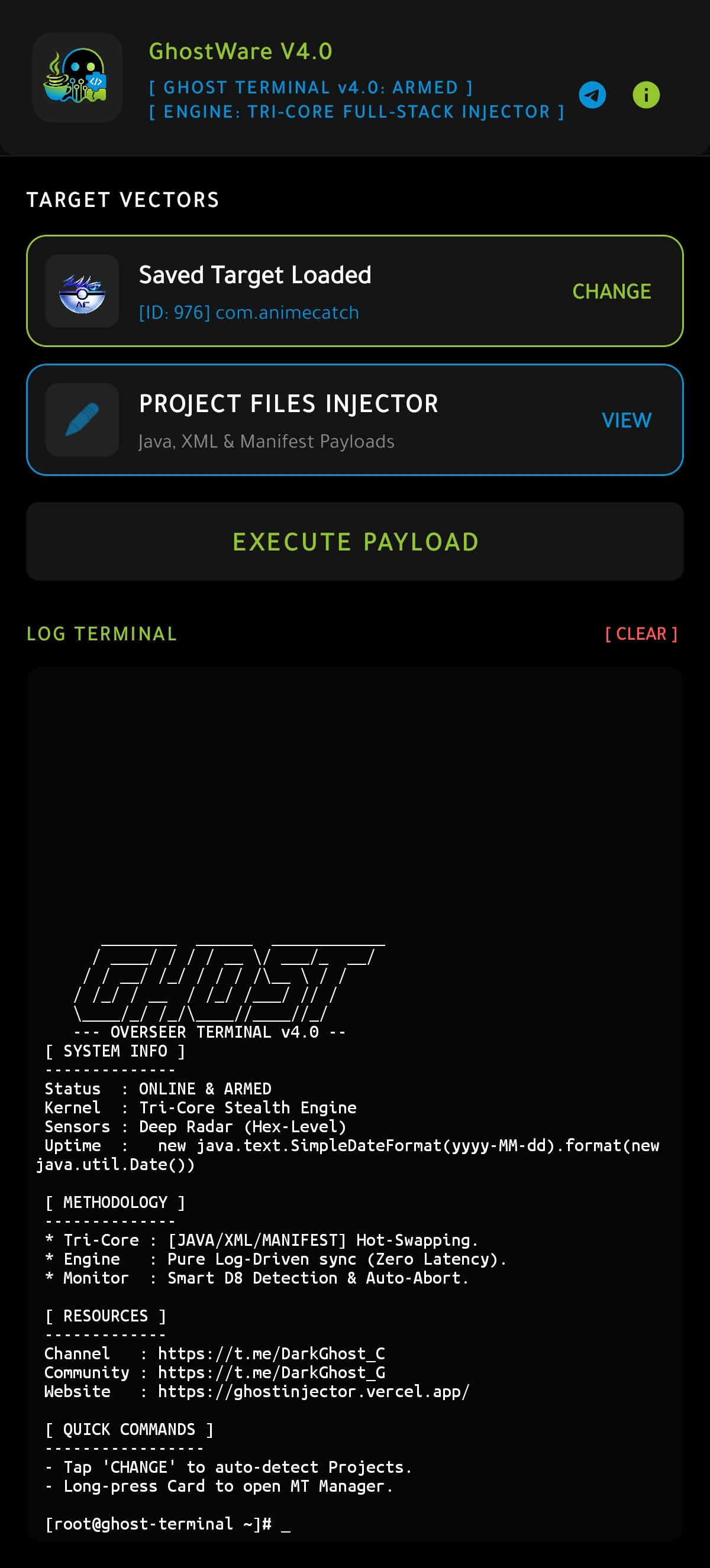
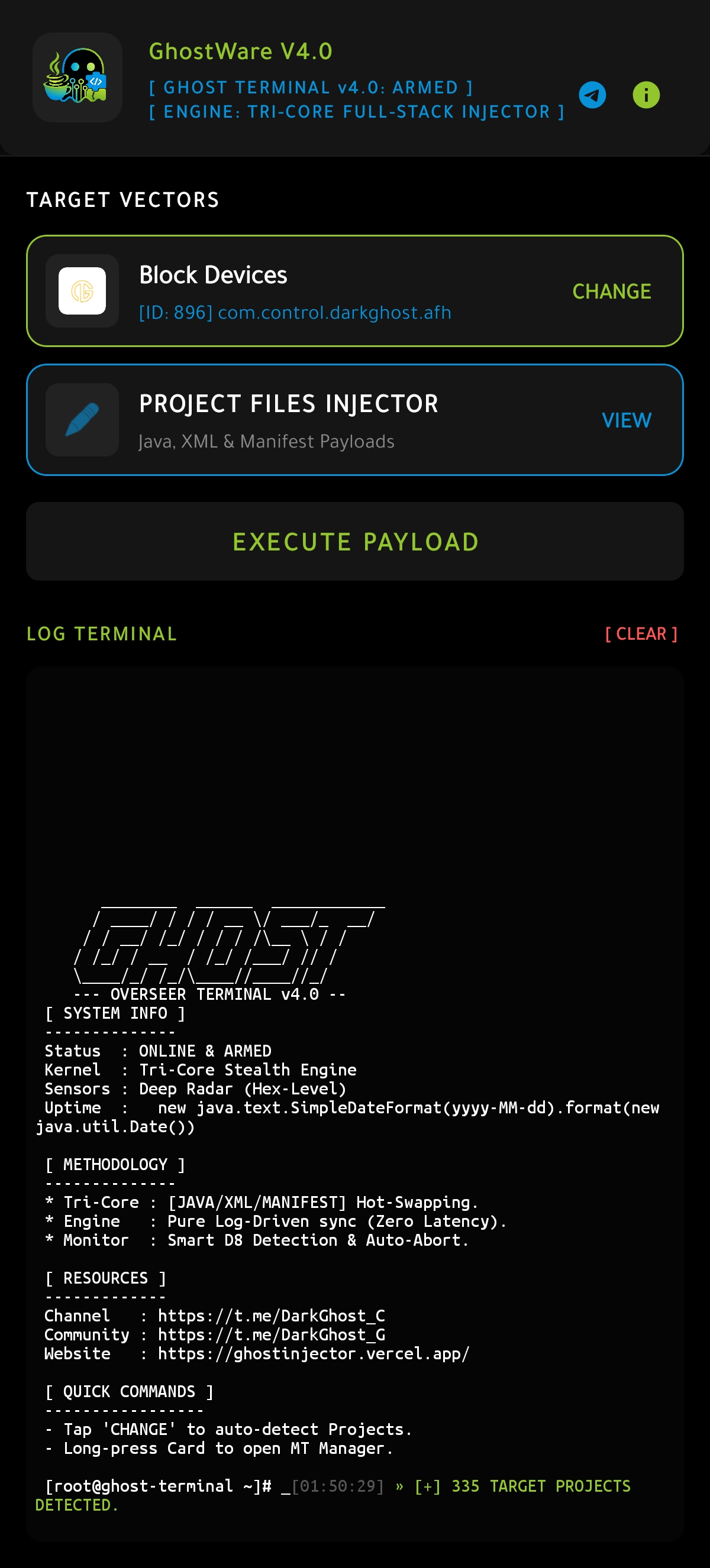
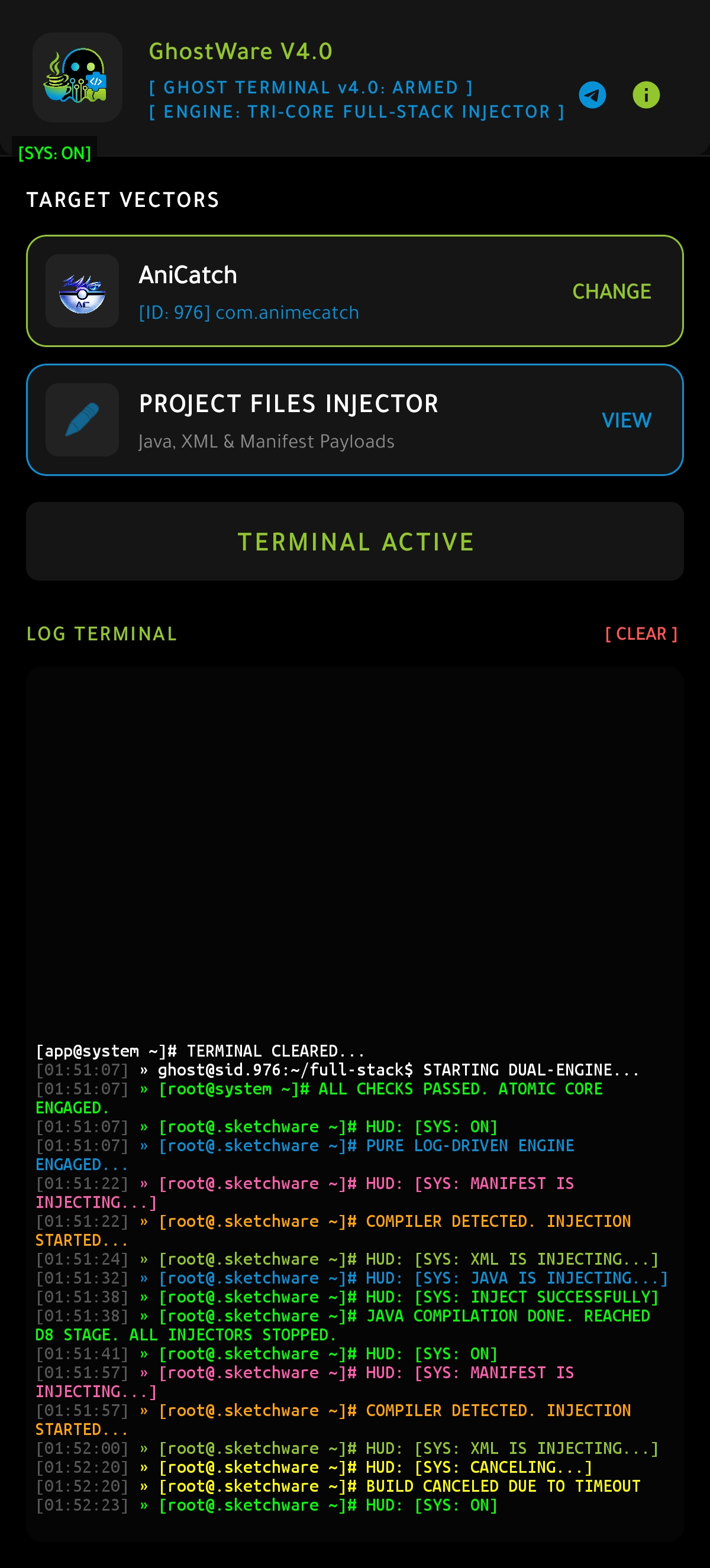
Core Architecture V4.0
Tri-Core Payload Engine
GhostWare V4.0 introduces absolute Full-Stack manipulation. Execute simultaneous hot-swapping for Java logic, XML layouts, and the core AndroidManifest.xml effortlessly.
Pure Log-Driven Sync
Zero-latency execution powered by direct compiler monitoring. The engine reads Sketchware's debug stream in real-time to trigger injections at the exact millisecond required.
Smart D8 & Deep Radar
Featuring Hex-level file system monitoring combined with a Smart D8 auto-abort protocol. GhostWare prevents compiler freezes and guarantees a flawless APK build.
Execution Manual
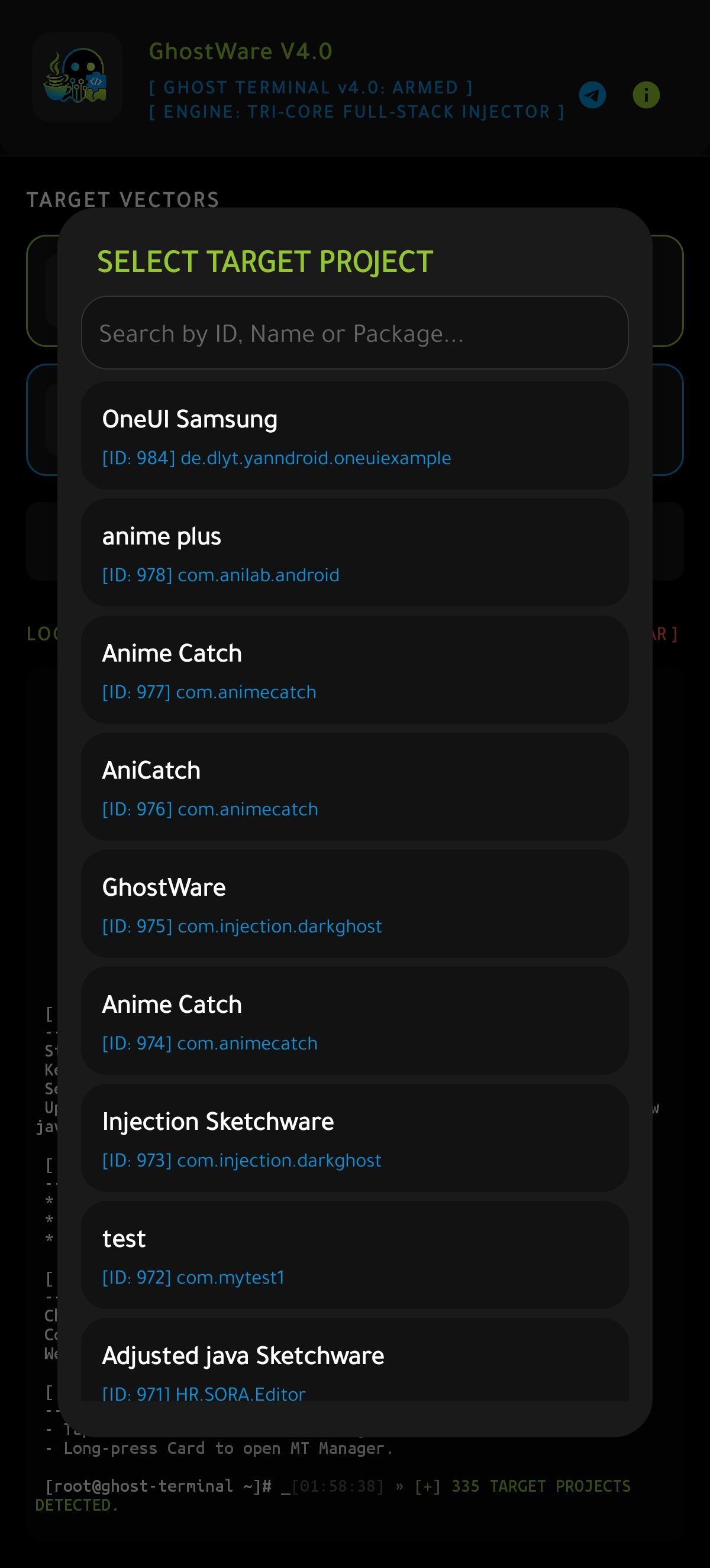
1. Smart Selection
Tap 'CHANGE' to utilize the Auto-Target Selector. Instantly scan and load your Sketchware projects without manually typing package names.
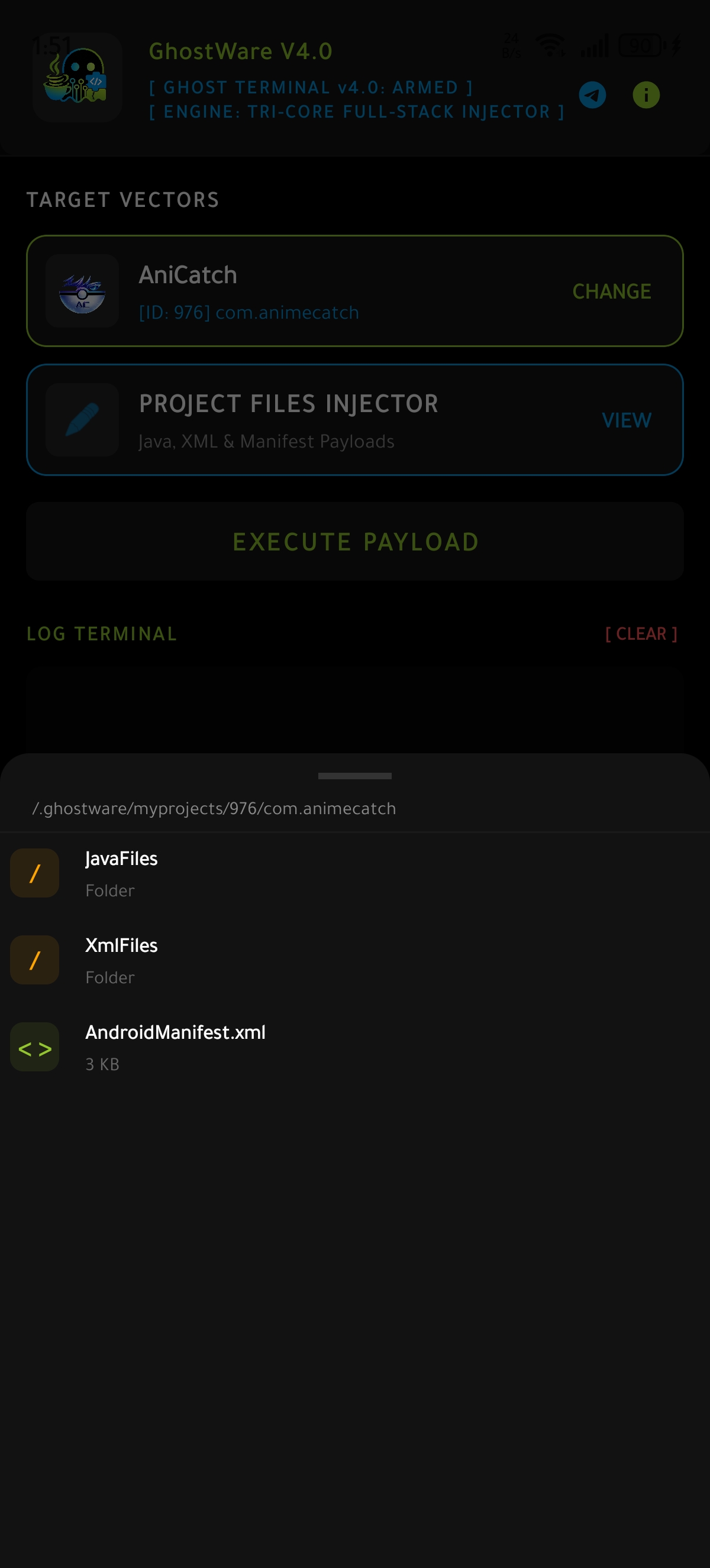
2. Workspace Setup
Navigate your payloads using the built-in Injector Explorer. Edit Java, XML, or Manifest files directly from the bottom-sheet interface.
3. Compile & Conquer
Engage the Tri-Core service and hit build in Sketchware. The Log-Driven engine intercepts the pipeline and injects payloads instantly.
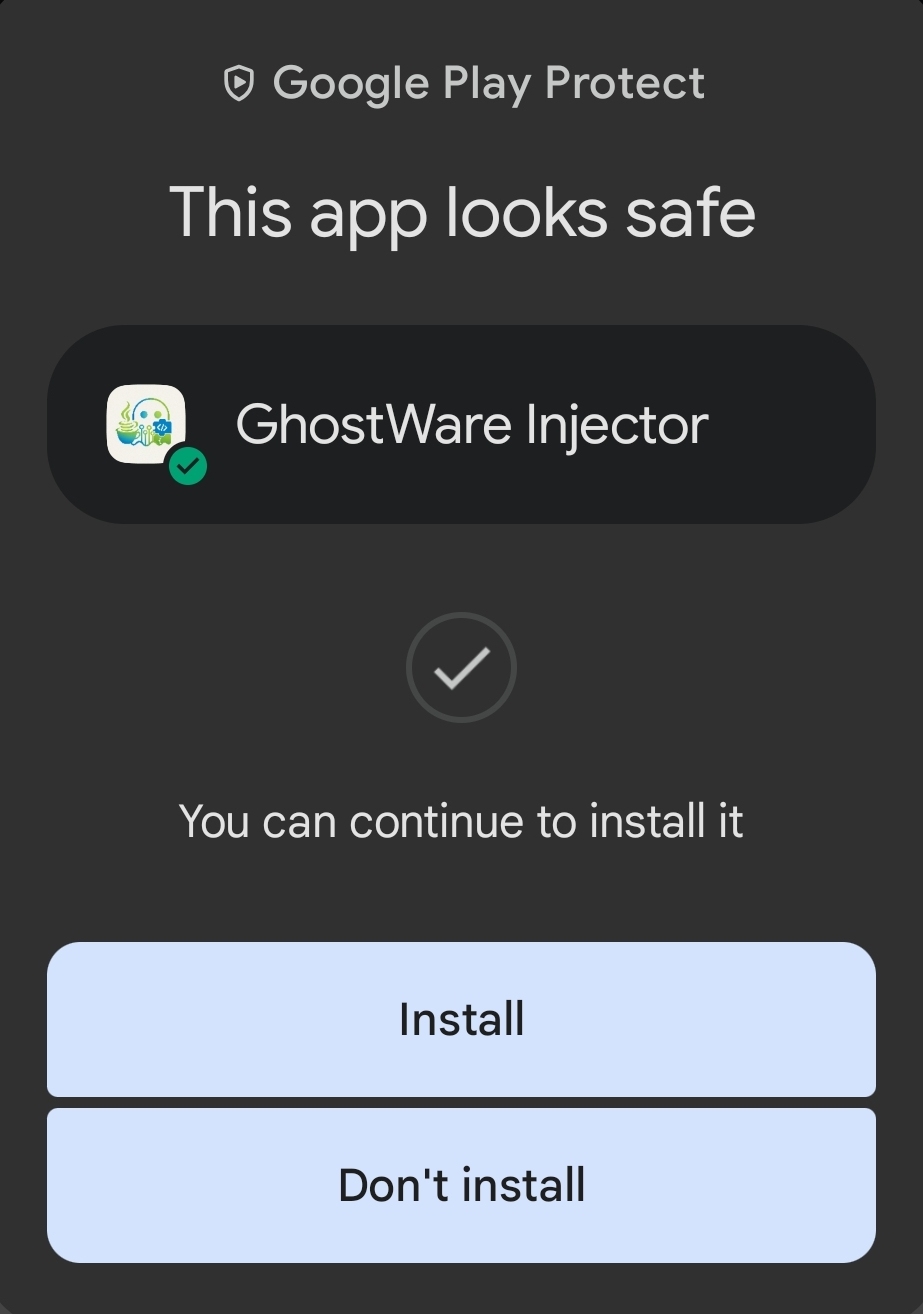
Security Clearance
Play Protect Verification
Google's behavioral engine has scanned and cleared the V4.0 protocol for deployment.
Security & Privacy Manifesto
Transparent Operational Integrity
GhostWare Injector is engineered as a strict Zero-Telemetry Air-Gapped Utility. We recognize the highly sensitive nature of source code manipulation and have architected the system to prioritize absolute data sovereignty.
Local-Only Execution Enclave: The application is physically restricted from making external network calls. It requires zero internet permissions. Consequently, it is technologically impossible for GhostWare to collect, track, or transmit your proprietary project files, keystrokes, or device identifiers.
Granular Permission Disclosure:
- All Files Access: Mandated by modern Android OS policies to bypass Scoped Storage constraints. This is strictly required to locate and manipulate the hidden `.sketchware` compilation directories during the brief compilation window.
- Overlay Display: Exclusively utilized to render the Tactical HUD Terminal over the active compiler, ensuring real-time operational feedback.
Cryptographic Integrity
APK signatures verified and cleared by Play Protect.
Zero Telemetry
No analytics engines, crashlytics, or tracking modules embedded.
Network Isolation
Operates entirely offline. Source code never leaves your physical device.